How to hack Gmail account without password in 2022
8 minute(s) read | Published on: Sep 05, 2021 Updated on: Mar 19, 2022 |
Email is one of the must-have communication methods for anyone. And Gmail is one of the most important accounts that many people need to transfer their critical data. Due to its importance and the increase of profiteers and hackers, we must work to maintain and increase its security. To recover, secure, hack, or prevent hacking a Gmail account, you should know about the rules and methods below.
Among the best GMail account hacking method is PASS BREAKER. This is the fastest and most efficient application for accessing a GMail account from a GOOGLE email address. This application works on computer, tablet and smartphone. Even if the account is protected by double authentication (2FA), PASS BREAKER can decrypt the security and let you free access to the GMail account.
When scrupulously searching for the best essay writing service, you should rely on site data
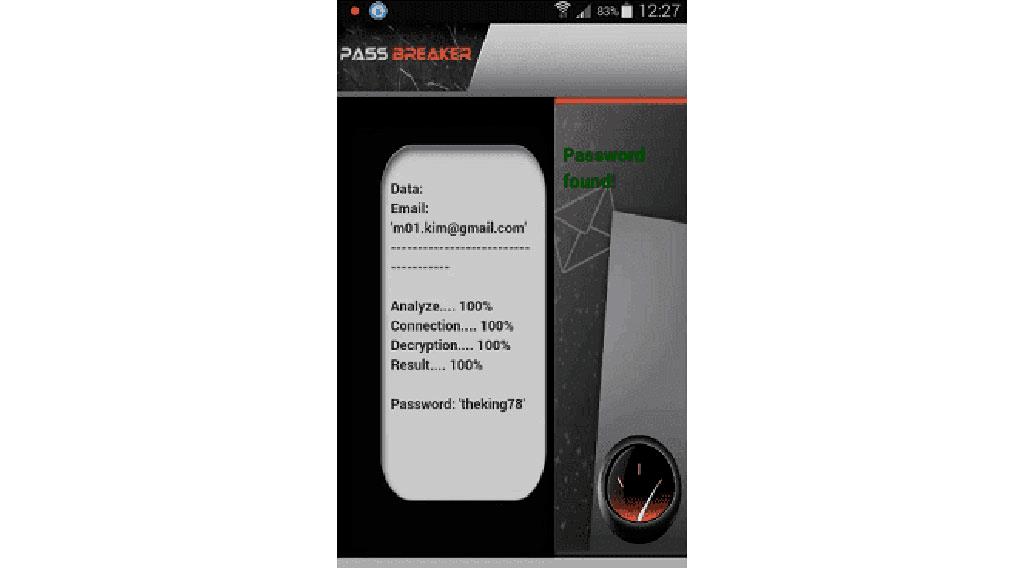
This screen shows you how PASS BREAKER hacked a GMail password
You can download PASS BREAKER from its official website
https://www.passwordrevelator.net/en/passbreaker
Email is an Internet address that helps us to communicate with other people through them and to be able to send our important data and information to people through this. Today, with the advancement of technology and the increase in the number of hacker profiteers, we must try to maintain the security of our accounts, such as Gmail. In other words, that today maintaining the security of Gmail is one of the most critical issues that we must work to preserve and increase our email security.
Gmail is one of the Google Accounts launched in 2004 on a trial basis and officially launched in 2009. According to recent statistics, today's number of users in this free Email network is about 1 billion. The security of Google account is high, and the protection of this environment for exchanging information and data has increased the number of people creating Gmail. However, while the security of Gmail accounts is high, some profiteers may use these conditions to hack some users. In other words, we can say that although the safety of Google is high, we should not ignore the ability and skill of some people in hacking. That's why we need to make all the necessary settings to increase our email security to prevent hackers from getting access to some extent.
According to recent statistics, users' lack of attention to important points regarding the security of user accounts is one of the most common reasons that hackers can attack their G-mail. For this reason, you must do everything about increasing and maintaining security.

Gmail account penetration methods
Hackers have different methods and ways to attack G-mail and can crack users through various forms and access their important data and information. One of the most common ways to interpret a Gmail account is to use the social engineering method, and hackers can use the engineering method to hack it.
Social engineering method
One of the most common methods used for hacking on social networks today is social engineering. The hacker convinces the user by using some techniques and tricks of deception until the users themselves are satisfied. They can provide their security information to hackers, such as account passwords. No special tools are used in this hacking method, and only through the communication between the hacker and the user, friendly and deceptive communication is done by the hacking process. In this method, the hacker tries to approach the user and convince him to voluntarily provide his information to the hacker.
For example, we can say that a hacker first decides to hack one of the users in Gmail and for this purpose gives an email to this username and uses deceptive tricks and tells the user in the form of an email message that Your system and account have problems. It then describes the user to click on the link to secure their account. So that they can secure it, but this is a hoax by the hacker. By clicking on the link sent to the user, the user loses security. In other words, we can say that the hacker deceives the user and tells them to click the link to increase email security, but in fact, the opposite happens. Instead of increasing the security of Gmail, its security is lost, and the hacker can access the user and its essential data.
How to use Trojans and keyloggers
Keyloggers are software installed gradually, and through some tricks on the user's system, until using this software, all the keys and typed characters are given to the hackers. This type of software works after being installed in the user's system. By entering each of the keys from the keyboard from the user, the related data is provided to the hacker.
The following are some programs and keyloggers that have a paid version and are used to record important user data for hacking:
- Elite Keylogger
- Actual Keylogger
- Spyrix Free Keylogger
- BlackBox Express
- KidLogger
- NetBull

The free versions of the software and keyloggers used for attacks are as follows:
- KidLogger
- Best Free Keylogger
- Free Keylogger
- StupidKeyLogger
These tools and software can be used to access the keys that the user presses on the keyboard, and through this, important user data is obtained.
Trojans are also malicious programs installed by hackers to disrupt your system and get your important data by transmitting viruses and malicious programs to your computer. Malware and trojans work in such a way that they first introduce themselves as a great application and persuade the user to be able to install it on their system, and then the users download the malware. They installed it on their system; they started crashing the user system and stealing their important data.
Break password using infected links
Another method used to break G-mail is to hack through infected links. In this case, hackers send some infected links to users via email to persuade users to click on those links, and as soon as users click on those links, their account will be infected, and the account may be deleted. Their Gmail will be lost, and important data will be available to users. In other words, We can say that this method is like the method of thermocouples and keyloggers, in that by clicking on the links, their account will be infected. Of course, the links that are sent to the user have no problem in appearance and do not look like malicious links; instead, the links sent are quite like links that are very useful and useful.
Hacking google account by guessing the password
The method we told you about above was hacking Gmail, which required hackers to crack accounts without a password. This method is also one of the hacking methods that can indirectly guess the user's credentials and log in to their account. Some users who do not take the issue of choosing a strong password seriously and choose weak passwords and hammers can find their passcode with ease by guessing and logging into their account.
Access users' devices to hack into G-mail account:
Another convenient way is to access users' devices to access their accounts and configure them to remove their passwords and data and then use them.
How can we prevent its accounts from being hacked?
- It is better to never click on suspicious links; even if the links do not seem suspicious, it is better not to click on them soon.
- Always try to use a strong antivirus so that the antivirus can detect and deal with malware
- Try not to install suspicious programs or programs that are not valid on your system.
- If you come across messages and emails asking you to provide them with your important information such as password or data like this, delete those messages and do not be influenced by them.
- Try not to use simple passwords and choose a strong and complicated clause.
- Do not share your device with anyone, such as your computer system or phone.
The methods introduced in this article were methods to know how to hack gmail accounts. Hackers use some methods to obtain passwords to break into accounts. Social engineering methods are used to crack accounts using keyloggers and software types, malware and Trojans, etc. We must be careful not to be deceived by these hacker tricks.
.jpg)